In this blog entry, I will summarize interesting articles I found on the net that explain all the different aspects of Secure Boot. If you are interested in UEFI Secure Boot and are wondering what it is, how it can help you, or simply would like to experiment with it, you are interesting in the following articles, blog entries etc. If you find other useful articles that should be mentioned please mention them in the comments below.
References
- SUSE and Secure Boot: The Details (SUSE)
- This article gives a brief overview of Secure Boot, how it works and the threats, Secure Boot will protect us from, and those, it will not protect us from.
- UEFI Secure Boot Guide (redhat)
- This article is more on the technical side, explaining how to configure typical computer on the basis of a Lenovo BIOS. It also gives requirements from Microsoft and gives an overview of the tools available for Linux.
- UEFI Secure Boot Mini HOWTO (ALT Linux)
- Explains the tools to use in more details and what needs to be done in order to get your own shim boot loader to be signed by Microsoft, including the different types of certificate one can use for the Microsoft submission.
- Managing EFI Boot Loaders for Linux: Dealing with Secure Boot (Rod Smith)
- Rod explains in this article how to set up the Secure Boot keys and how to sign and verify UEFI boot loaders.
- James Bottomly’s UEFI Secure Boot Page (James Bottomly)
This describes how to use Tianocore and the qemu pages to set up virtual Secure Boot development environment and some tools to use for creating keys, signing etc. His accounts for going through the Microsoft Signing process can be found in the following blog entries: Adventures in Microsoft UEFI Signing and Linux Foundation Secure Boot System Released.
- Building a UEFI Secure Boot Enabled Virtual Machine (Tom’s Blog)
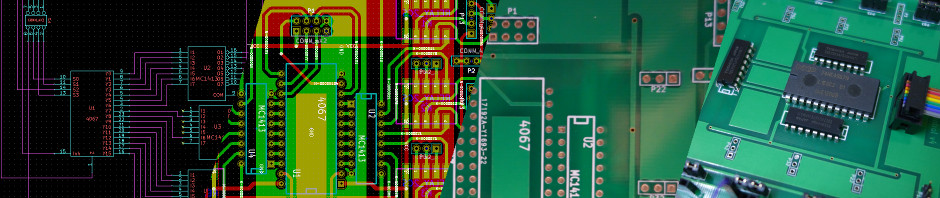
- In an earlier article I explained how to compile the Tianocore UEFI BIOS so that it can be readily used in combination qith QEMU.
- Pre-submission testing for UEFI submissions (Microsoft)
- This article explains how Microsoft suggests that UEFI submissions should be tested prior to submitting them to Microsoft. This article also links to “Signing UEFI Applications and Drivers for UEFI Secure Boot” (cached copy), an excellent guide of what needs to be done to set up a virtual environment for your own Secure Boot experiments.
- Microsoft UEFI CA Signing policy updates (Microsoft)
- This blog entry discusses Microsoft’s current signing policies. It pretty much is a list of requirements that a UEFI Submission should adhere to for Microsoft to sign it. Or if signed and determined to have been violated, reasons for Microsoft to blacklist your submission.
- Windows 8.1 Secure Boot Key Creation and Management Guidance (Microsoft Technet)
- This article describes all aspects of key generation and management. This seems to mostly apply if you are a BIOS vendor.
Pingback: UEFI Secure Boot: Hands-on Experience | Tom's Blog